Blog Severedbytes.net What It Is, Who Runs It, and What You'll Find There
Share your love
Blog severedbytes.net is an independent technical platform that publishes guides on system security, network configuration, and privacy tools. It runs without advertising, affiliate links, or sponsored content and the person behind it stays anonymous by design.
What Is Blog Severedbytes.net?
At its core, this is a single-author technical blog aimed at people who already know their way around a terminal. Not a media company. Not a content team optimizing for traffic.
Just documented, tested implementations of real infrastructure work.The platform covers a focused set of subjects: Unix security, firewall configuration, VPN setup, encrypted DNS, server management, and open-source tooling.
If you're looking for product reviews, gadget roundups, or commentary on the latest software release this isn't that.What's often overlooked is how deliberately narrow the scope is.
That narrowness is the point. In practice, most independent tech blogs try to cover everything and end up shallow on all of it. Severedbytes takes the opposite approach.
Who Runs Blog Severedbytes.net?
The blog is operated by an anonymous systems engineer. No name, no LinkedIn profile, no personal brand attached to the work.That might seem unusual. And honestly, it raises a fair question: if you can't verify who wrote something, how do you evaluate whether to trust it?
The answer here is practical rather than philosophical.The content is procedure-based step-by-step guides that either work in a real environment or they don't. Readers who test the configurations either get the result or they don't.
The author's identity doesn't change whether the firewall rule fires correctly.That said, anonymous authorship does have real limits. There's no way to verify credentials, professional history, or potential blind spots.
Readers should approach the content as they would any technical documentation, test it, verify it in a non-production environment first, and apply independent judgment.
What Topics Does Blog Severedbytes.net Cover?
System Security and Unix Administration
This is the heaviest coverage area. Articles address privilege escalation prevention, permission management, hardening procedures, and kernel-level diagnostics. The tone is operational written for someone configuring a real system, not studying for a certification exam.
System administrators who deal with production Linux environments will find this section the most immediately applicable. The guides don't pad out with background theory they get to the configuration steps quickly, with troubleshooting notes included.
Network Configuration and Firewall Setup
Netfilter configuration, packet filtering, traffic shaping, and bandwidth management all appear here. There's also coverage of home lab hardware selection, which is useful for readers building test environments on a budget.
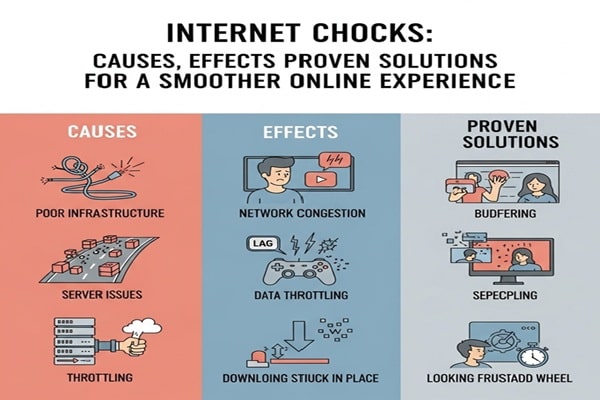
Gaming network optimization gets attention too latency reduction and connection stability through configuration adjustments rather than hardware upgrades. A slightly unexpected topic for a security-focused blog, but it reflects practical use rather than thematic purity.
Privacy Tools and VPN Guides
Privacy-focused networking is covered with more depth than most comparable blogs manage. VPN protocol comparisons, encrypted DNS options, and anonymity tool evaluations appear regularly.
What makes this coverage useful in practice is that it examines trade-offs rather than just listing features. Choosing between WireGuard and OpenVPN, for example, involves performance, security posture, and use-case context, not just which one is newer.
As reported by Ars Technica, WireGuard was found to be notably faster to set up and reconnect than existing protocols like OpenVPN, while noting that protocol selection ultimately depends on your specific environment and requirements.
A distinction well documented as reported by Ars Technica, which found WireGuard faster to set up and reconnect while noting that protocol selection ultimately depends on your specific environment and requirements.
Open-Source Solutions and Server Management
RAID configuration, backup automation, data recovery, migration procedures, and legacy system maintenance all appear in this section.The guides tend to be long-form, with error handling and edge cases documented alongside the main procedure.
What the Blog Doesn't Cover
Worth being direct about this: there's minimal trend coverage, no product launch commentary, and limited GUI-based tutorials. If your workflow is primarily graphical or if you're looking for coverage of cloud platforms like AWS or Azure this blog isn't oriented toward that.
How Blog Severedbytes.net Maintains Editorial Independence
No Advertising or Affiliate Programs
The platform rejects advertising and sponsored content. Product and tool recommendations aren't tied to affiliate tracking which, for a blog recommending privacy and security tools specifically, matters more than it might on a general tech site.In practice, most independent tech writers find that once affiliate income becomes meaningful.
It quietly shapes topic selection and framing according to The Guardian, which has itself published a detailed explainer for readers noting that affiliate commissions can influence which products receive coverage across digital publishing. Severedbytes removes that variable by not participating in affiliate arrangements at all.
How the Blog Is Funded
Three mechanisms support the platform:Liberapay, an open-source donation platform that allows recurring voluntary contributions. No fees taken by an intermediary on the standard tier.
Monero contributions Monero is a privacy-preserving cryptocurrency. Using it for donations fits the platform's stated philosophy: readers who care about financial privacy can support the blog without that transaction being traceable on a public ledger.
Pay-what-you-want script downloads scripts documented in articles are available for download with optional payment. You can get them free or contribute what you think they're worth.
The funding model covers hosting and operational costs.Any surplus reportedly goes toward related open-source projects.There's no advertising revenue to fall back on, which keeps the editorial logic clean but it also means the platform's continuity depends entirely on voluntary reader support.
No User Tracking or Analytics
No analytics platform runs on the site. No user profiling, no tracking pixels, no third-party scripts collecting behavioral data. For a blog explicitly about privacy, running surveillance-grade analytics would be a hard contradiction.
How Content Is Written and Maintained
Every procedure documented on the blog is tested before publication.That's not a claim unique to Severedbytes,most technical blogs say the same but the documentation style reflects it.
Articles include actual command outputs, error scenarios encountered during testing, and specific troubleshooting steps that only appear when someone has actually run the procedure.
Updates happen through article revision rather than new posts.
When a software version changes or a security recommendation evolves, the existing article gets updated with revision notes explaining what changed and why. This is a better model for reference content than publishing a new post each time something shifts.
The writing style assumes command-line proficiency. There's minimal hand-holding on basic concepts. If you encounter a term you don't know, the expectation is that you'll look it up independently rather than find it explained inline. That won't suit everyone but it keeps the articles tight and avoids the padding that dilutes a lot of technical writing.
Who Should Actually Read This Blog?
The realistic audience is fairly specific:
- System administrators managing Linux-based infrastructure
- Home lab builders who want tested configurations rather than theoretical guides
- Privacy-focused users who want implementation detail, not just product recommendations
- Security researchers looking for baseline configuration references
Is it useful for beginners? Partially. Someone early in their Linux learning who is comfortable with the command line and willing to do background research independently can get value from it.
But if you need concepts explaining from scratch what a firewall is, why a VPN works the way it does you'll likely want to build that foundation elsewhere first before the articles here click properly.
How Blog Severedbytes.net Differs From Ad-Supported Tech Publishing
The structural difference is straightforward. An ad-supported publication needs traffic volume to generate revenue. That incentive pushes toward broader topics, more accessible writing, trend coverage, and content calendars optimized for search volume rather than technical usefulness.
Severedbytes doesn't have that incentive. Publication follows quality rather than schedule. Topics get covered because they're technically important, not because they're trending. Interestingly, that occasionally means covering subjects with low search volume that would never make a commercial editorial calendar but that practitioners actually need documented.
The trade-off is frequency and breadth. You won't find daily posts here. The content library is focused and slow-growing, updated carefully rather than expanded constantly.
Community and Reader Engagement
There are no forums, social media channels, or comment sections in the traditional sense. Community engagement happens indirectly,readers implement the procedures, adapt them for specific use cases, and reference the articles in their own documentation or projects.
This decentralized model has one practical advantage worth noting: the content isn't hostage to any platform's policy changes or service shutdowns. An article published on the blog remains accessible regardless of what happens to Twitter, Reddit, or any other centralized platform where discussion might otherwise live.
For readers who want to follow new content, this setup does require more effort. There's no algorithm surfacing new posts. You either check back directly or use an RSS reader if one is available.
Conclusion
Blog severedbytes.net is a narrow, deliberately independent technical resource. It covers system security, networking, and privacy without ads, affiliates, or tracking. Useful for intermediate-to-advanced Linux users who want tested procedures over polished content.
Frequently Asked Questions
Is the blog severedbytes.net free to read?
Yes. All articles are publicly accessible without login or subscription. Some scripts mentioned in tutorials are available as optional pay-what-you-want downloads, but the written content itself is free.
Who is behind the blog severedbytes.net?
The blog is run by an anonymous systems engineer. No personal identity is attached to the platform. The authorship model is intentional; it keeps focus on content rather than personal brand.
What skill level do I need to use this blog effectively?
Intermediate to advanced. You should be comfortable working in the command line and able to research unfamiliar concepts independently. The guides do not explain foundational concepts inline.
Does the blog accept guest posts or contributions?
This is not publicly confirmed. No formal submission process is documented. Contributions, if they happen, appear to occur informally rather than through an open editorial pipeline.
How do I support blog severedbytes.net?
Through Liberapay donations, Monero cryptocurrency contributions, or pay-what-you-want script downloads. No other formal support mechanism is publicly stated.

![The Rising Popularity of the Swimsuit Edition [ABBB] – 1.20 21 Swimsuit Edition – Chapter](https://misstechy.com/wp-content/uploads/2025/09/w12-min.jpg)